Help AG’s Cloud Security services deliver a comprehensive suite of technologies and practices designed to govern identities, restrict networks, protect data, and secure workloads, all as part of our cloud security consulting, ensuring compliance with essential governance frameworks
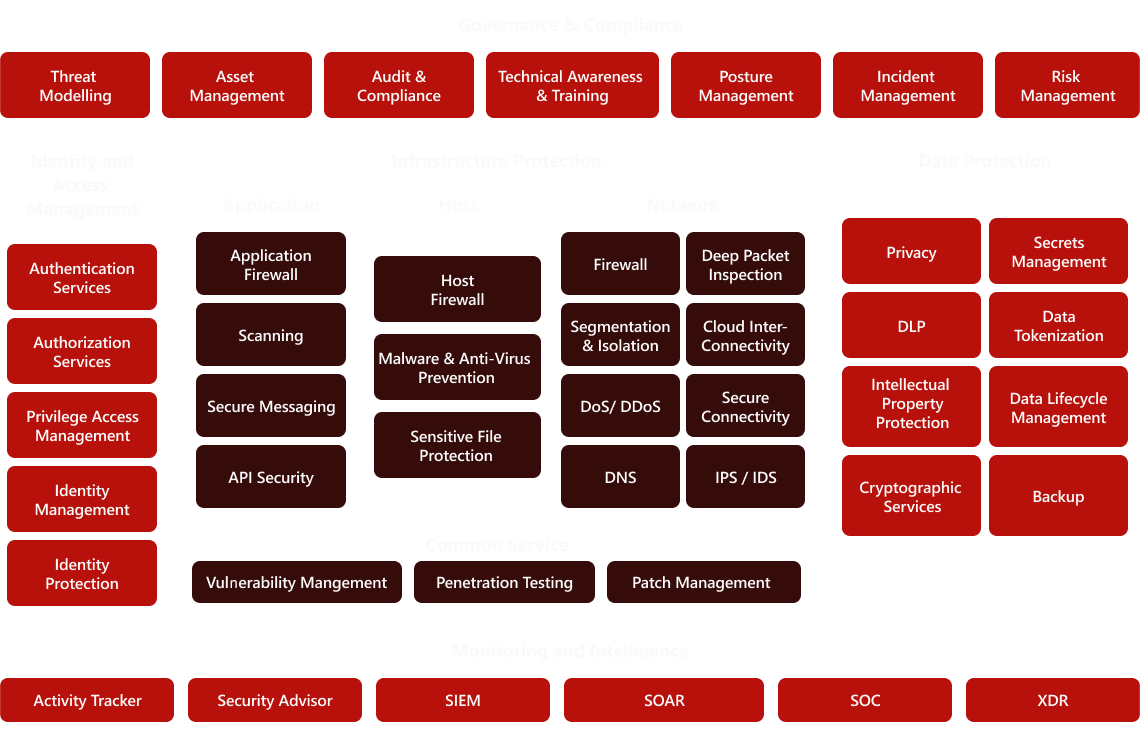
We cater to a wide range of cloud security needs
Provides comprehensive protection against a wide range of cyber threats.
Reduces costs associated with data breaches and regulatory fines.
Streamlines security management across complex, multi-cloud environments.
Provides comprehensive protection against a wide range of cyber threats.
Reduces costs associated with data breaches and regulatory fines.
Streamlines security management across complex, multi-cloud environments.
We partner with leading vendors to deliver cutting-edge cloud security solutions:
Partnered with top-tier cloud security
technology providers.
At Help AG, our specialized cloud security assessments are delivered by certified cloud security professionals, positioning us as a leading cloud security company with industry-leading expertise and giving you peace of mind in your cloud environment.
SaaS sprawl is real — and so are the risks that come with it. We assess your third-party SaaS platforms for configuration gaps, weak access controls, API risks, and data leakage vectors. Whether it’s your CRM, HRMS, or collaboration tools, we help you secure your SaaS footprint without slowing the business down.
Whether you're on AWS, Azure, or GCP — cloud misconfigurations are a leading cause of breaches. Help AG’s cloud review inspects IAM policies, workload protection, logging, encryption, and more. We map your cloud posture to industry standards like CIS, NIST, and CSA, giving you a clear view of risks and remediation priorities.
Your productivity suite shouldn't be a security liability. Our Office 365 assessment dives into tenant configuration, access controls, data loss prevention, email security, and advanced threat protection. We ensure your Microsoft 365 environment is fortified, compliant, and well-guarded against phishing, account takeover, and data exfiltration threats.
Security starts with sound design. Our architectural reviews evaluate your network, system, and application architecture against zero-trust principles, segmentation strategies, and threat models. We uncover systemic risks, misaligned trust boundaries, and legacy dependencies — and provide recommendations that modernize and harden your environment.
Get under the hood of your security stack. We perform detailed configuration reviews across key infrastructure components (firewalls, endpoint platforms, VPNs, proxies, etc.) to ensure they align with industry best practices and your organizational threat profile. Misconfigured systems are often the low-hanging fruit for attackers — we help you take them off the menu.
Analyze your cloud architecture to ensure it is designed with robust security principles and best practices.
Review the security measures of your SaaS applications to ensure they meet industry standards and protect against threats.
Evaluate your overall cloud security stance, identify vulnerabilities and get actionable improvement recommendations.


Speak to our cybersecurity experts to safeguard
your infrastructure.
securing customers’ digital journey & fortifying cyber defence.
offering an end-to-end portfolio of services that are catered to securing devices.
where creativity meets cutting-edge innovation to drive transformative solutions.
protecting your cloud infrastructure with cutting-edge security solutions.
insights and analysis on the latest trends & technologies.
stay updated with our latest news, press releases, & more.
in-depth research and analysis on key cybersecurity topics.
watch & learn from our insightful video gallery
critical updates and alerts on emerging threats.
comprehensive guides and technical documents.
Real-world examples of our solutions in action across industries.
Real feedback and impact from our customers' experiences.
These are the zero-day vulnerabilities discovered.