DIGITIZING DNA! COULD THIS BE THE FUTURE OF STORAGE?

In my last blog, I discussed an ingenuous technique by which researchers had managed to carry out an attack using DNA! While that no doubt sounds like something from the realm of science fiction, it’s definitely not the only way the digital world is being integrated with DNA. The security of confidential information has never […]
WPA2 KRACK ATTACK THREAT ADVISORY

Until recently, WPA2 was considered to be the most secure and reliable wireless network protocol over others such as WEP, and WPA.v1. The security community has however now uncovered the KRACK attack which undermines the authentication and encryption of the WPA2 protocol, thereby negating its security benefits. Key Reinstallation Attacks (KRACK) work against all modern […]
HUMAN DNA USED FOR HACKING – THE DAWN OF NEW ERA IN CYBERSECURITY?
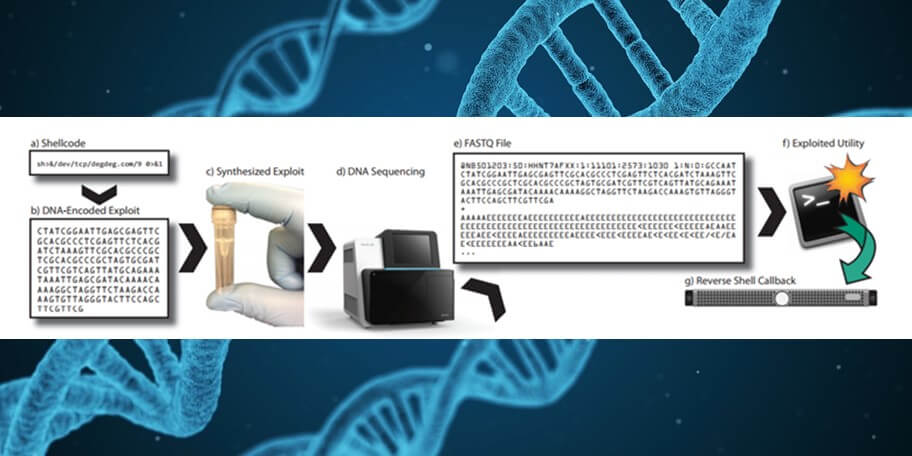
While the constant creativity demonstrated by cyber criminals often leaves people wondering about the future of cyber-attacks, a weird and frankly, pretty scary way has recently come to light- and it’s using DNA! Yes, you read that right. First question, why would anyone want to hack DNA? Well for starters, if you have been watching any […]
LET’S START AT THE END(POINT)

Cyber security encompasses a number of solution, policies, procedures and practices- and it’s a list that keeps growing as cyber criminals fine tune their strategies and find new and innovative way to target enterprise IT systems. One such area where there truly is a lot of interesting stuff happening is at the endpoint. If we […]
EMPLOYEE PROFILE: MUKHAMMAD KHALILOV

Designation: Principal Security Analyst & Manager of Security Analysis Team Number of Years at Help AG: 4 Q) What made you chose a career in IT? I have always been interested in tinkering with digital gadgets. IT offers diversity and never-ending challenges, which translates to a never-ending learning path and constant stimulation. Being in IT, […]
SMART CITIES NEED SMART DATA PROTECTION

Smart city initiatives are primarily driven by regional Governments which must also play a key role in establishing the security frameworks required for these initiatives to succeed. An area where government can and should get involved is in awareness of the general population. Especially in our region, with the cultural diversity coupled with the tremendous […]
PETYA RANSOMWARE THREAT ADVISORY
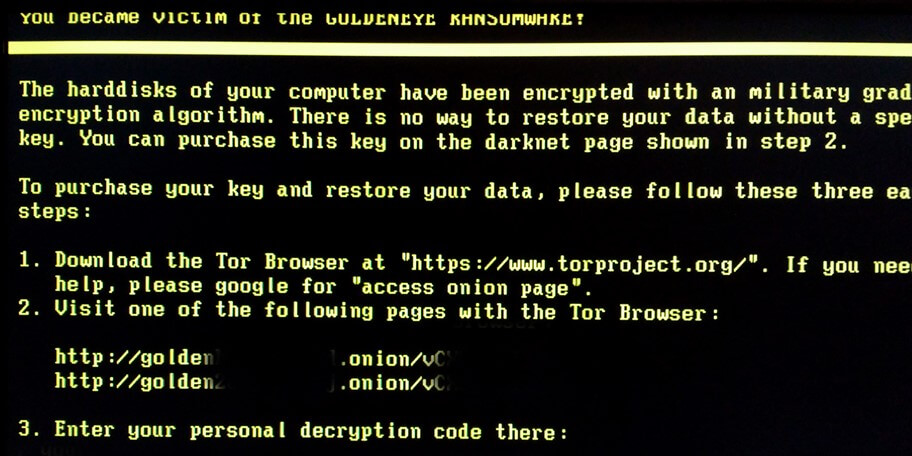
Petya was first reported in March 2016, and what we see now is improved version also referred as “NotPetya” or “GoldenEye”. It is a nasty piece of ransomware and works bit differently from any other ransomware or malware in that it does not encrypt files on a targeted system one by one. Instead, it reboots […]
MAKING SECURITY ANALYTICS WORK FOR YOUR ORGANIZATION
In recent years, there have been significant changes in hackers’ motivations and the ways they approach their objective(s). Whereas malware used to be the common focus, we now see hackers utilizing legitimate tools in combination with stolen credentials. As a result, today, many threats cannot be detected without deep insight! Analyzing the tremendous volume of […]
OUTSOURCING SECURITY? HERE’S 6 TIPS FOR SUCCESS!

In recent years, numerous high-profile attacks and countless more unreported security breaches have placed cyber security front and centre in IT discussions. Every CEO wants to hear a resounding “yes” from their CISO in response to this critical question- “Are We Secure?” Unfortunately, as much as I wish I could say otherwise, I know with […]
FIREBALL MALWARE THREAT ADVISORY

Recently a new malware named Fireball was been reported which acts as browser hacker. It is reported to have infected over 250 million computers around the world. It is believed that the malware is designed to be adware as part of advertisement campaign by Rafotech, a Chinese marketing firm. The malware mainly infects computers by […]