In the past years we have seen a massive rise in hacktivism, with specifically anonymous publishing target list after target list.
Probably the most well known was the original campaigns around the original WikiLeaks – Since then we have had to battle with #OpPetrol, #OpDjioubuti, #OpSaudi, #OpHere, #OpThat…

While I can really understand there is a lot of things hacktivist may have a problem with a lot of things, where they may want to express themselves through DDOS tools and defacement exercises – But they must also see when there is so many campaigns going it is very difficult to drum up support and activities on the same.
If we take some of the recent campaigns as an example, and here I am specifically thinking of #OpDjibouti – That campaign targeted close to 200 private and public organization in the UAE – While some sites were effected, the results were no where as severe as we have seen in the past…Is that because there is less attackers or because they are spreading themselves too thin…or would it have happened that it customers have actually been better at protecting themselves – Or is it a combination?
First of all I think the majority is down to the targets being spread too thin – Which means that when Anonymous targets their guns at someone the barrage is not concentrated enough – You need to understand that most hacktivist groups are not structured organizations with a lot of top-level control and coordinating attacks are difficult – Anonymous communicate via pastebins, which are unorganized micro web-servers intended to publish pasted information between individuals or a group of individuals. The pastebin is also typically where the hacktivists will be publishing whatever bounty they managed to get.
As such a pastebin does therefore not give any control of who sees it or who has access to it – which to some extend is very much in line with the spirit of the hacktivists.
The links to the different pastebins containing the campaigns are then distributed via twitter or some other means of communication such as IRC channels – Mostly as these communication forms allows for a quick distribution of the message and the ability to reach a lot of people, however again there is no guarantee for delivery or participation in a campaign by the hacktivists…
Finally, if the hacktivists receives the campaign there are also an chance that they do not want to participate – Recently we saw this during the Crimea conflict, where hacktivists from both sides where fighting each other…
In short, being a hacktivist group is not an easy job, especially not if you want to be in control, which is required to be successful.
Should I worry then?
So should you worry about the hacktivists when they are so unorganized? Unfortunately yes, as hacktivists are trying to harness the power of cloud computing to become more efficient – Why worry about organizing the attacks if you can just create weapons so powerful that the destruction power is so great that one or two attackers can do more damage then any group of individuals could in the past.
Such tools are called Booters, or DDOS-for-hire. There are numerous ones available and they are ready to arm their guns at any organization or website…
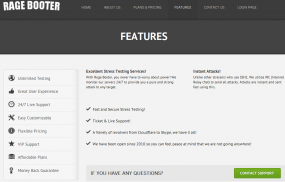
This is a screendump from rage-booter a fairly old site, which does not operate anymore.
The funny thing is that most of these services are legitimate run applications, which are sold as Web-site stress testing tools, and then there are the ones on the dark side of the web, which are operated with pure destruction purpose.
The economy behind these are difficult to understand, however the services are there and a lot of new ones is popping up, which again is an indication they are used.
So what can you do?
When talking to customers I always recommend that you do most with what you have, which means you need to understand how would you be affected and how can you increase your robustness – It is fair to say that hacktivism is today a persistent background noise we need to accept when we are connected to the internet and making our presence published through web-sites and applications.
You need to understand that the internet is a bit like a fruit orchard – The lowest hanging fruits are being picked first – Therefore you should make sure are not one of those low hanging fruits – If you are even down-fallen fruit lying on the ground ready to be picked up you are simply asking for it…
In Help AG we look very seriously at exactly these topics, and protecting against hacktivism is something we deliver services for through our managed services, where we focus on ensuring you have the correct level of robustness as well as agile remediation services in case the issue should happen – This means that in case you are under attack or your web-site is defaced we can ensure that your website is replaced by non-offending content within seconds instead of you having to get your web-administrators to replace content or restore backups, which could be an exercise that takes hours.
Consumer electronics and how it affects security?
Today everyone runs around with a super computer in their pockets. It is staggering, my smartphone has 10’s of times more power then the BigBlue Supercomputer which beat Kasparov in the late 90’s…
Why is this important? Well at Help AG we utilize these kind of capabilities to enhance our services. Spending less then 15.000 AED we built a super computer of off-the-shelf hardware, which has computing power that just a couple of years ago was unthinkable.
We call it the Crackodile, and it bruteforces 50 Million password combinations per second it runs! How does it impact you – Well the way that you create and utilize your password policies is something that changes – If we go on like this a password is no where near enough in the future!
You may be interested in the following article on the same.
Just to start your thought process please also see the below infographics from Experts Exchange – Mind blowing…







