Over the past few months, I have seen a significant increase in talks on social media and in the news regarding “people’s health” (i.e. employees) and culture in the workplace. More recently, my peers and especially fiends in cybersecurity have reminded me of the importance of a healthy culture – a set of expectations that influence behavior as well as surround and pervade our teams. I believe a healthy work culture is an investment in your cyber resilience.
Our customers benefit from a healthy work culture in many ways. Firstly, a toxic or unhealthy work culture creates divisions, tension, and siloed teams – getting things done is hard, communication is difficult, conflict is frequent, and delays are constant. The opposite is true for a healthy culture.
What many leaders fail to realize is that there is no middle ground – there is no “OK” culture that exists between an “unhealthy” and a “healthy” one. Your organization’s culture is either healthy and being cultivated to continue in this way, or it is heading towards being unhealthy and possibly toxic.
At Help AG, a healthy culture is vital to ensure we are operating at our best. It also ensures individuals are supported when difficulty raises. When dealing with cyberthreats, attacks and critical incidents, it is too late during an incident to attempt to build a healthy work culture! This work, during what incident responders call the “preparation” phase, occurs long before a cyberattack or incident is experienced. The right preparation ensures teams and individuals are empowered to make decisions quickly. Quick decision making significantly reduces the impact of cyberattacks, improves time to detection, and enhances the overall mitigation and response process.
As a result of the healthy culture that Help AG built over the years, we have been able to serve our customers with speed, agility, and excellent quality during the new normal. We retained our workforce and continue to expand our team size and customer base. A healthy work culture requires hard work and focus on the ight behaviors by everyone, especially those in leadership. At Help AG, our investment in our work culture is an investment in the resilience of our customers. It is integral to who we are.
I wish you all the success as you build a healthy work culture, improve your cyber resilience, and empower your teams.
Top Cyber Threat in Q2 2021
Print Services Under Attack
In late June 2021, reports regarding a critical vulnerability in the Windows Print Spooler service were validated and Microsoft released multiple updates to address the vulnerability (CVE-2021-34527).
This vulnerability permitted a remote attacker to compromise a vulnerable system, and at the time of release the vulnerability was already being publicly exploited. Help AG, alongside many in the cybersecurity community, noted that the patches were important. However, on vulnerable systems, attackers could still gain a foothold if certain settings were not present.
Help AG Recommends:
- Disable remote print spooling on and to endpoints that are not Print Servers.
- Apply patches to all affected systems.
- Monitor for creation of new local accounts, especially administrators.
- A Windows system may still be vulnerable following installation of the appropriate patch. Carefully review Microsoft’s advice regarding this.
Targeting of Logging and Monitoring Tools
The REvil ransomware group continues to build notoriety through an escalation in attack sophistication. A recent repot from Huntress Labs describes the TTPs used by REvil against many Managed Service Providers (MSP), all of whom believe they were compromised through a vulnerable Remote Monitoring and Management (RMM) product from Kesaya.
Many MSPs also witnessed efforts by REvil crew to disable and disrupt monitoring and auditing of malicious activities. In particular, PowerShell was used by the REvil crew to cripple Windows Defender, whilst leaving it unning and operational, using the ”Set-MpPreference” Cmdlet to disable monitoring, intrusion prevention, script scanning, network protection and submission of malware samples.
Help AG Recommends:
- Train analysts to identify malicious administrative activity.
- Monitor for changes to detective and protective controls across endpoints, especially EDR.
- Identify and validate changes to systems that disable logging or auditing.
Cybersecurity solutions under attack
During Q2 2021, Help AG saw an increase in threats, attacks, and vulnerabilities in cybersecurity products.
These vulnerabilities were detected, published, and in some cases exploited in cybersecurity products like SonicWall, PulseSecure, TrendMicro APEX1, VMware Carbon Black, PAN Cortex XSOAR and Cisco ASA.
Cybersecurity products will continue to be targeted and exploited.
What can you do about it?
- Scan, Patch and Protect your Controls.
- Implement PAM and Monitor for Bypass Attempts.
In some organizations, cybersecurity controls can sometimes feel like they are ‘invincible’ (i.e. they do not require updates or patches like other assets). This is dangerous, and yet the belief persists.
Firstly, every system needs care and attention. This means keeping the software and firmware elements updated to fix vulnerabilities. If there is a concern about impact on your business (if the system is rebooted or ‘down’ due to the update process), this should dive a re-design or re-architecting of your security controls so they can be updated without influencing business operations (e.g. NGFW, WAF). It is unlikely that your board or senior leadership will accept that it was “too hard”, or that patching “might cause an impact”. The impact of ransomware or a cyberattack is extremely likely to significantly affect business operations and cause damage to reputation, requiring crisis communication.
Help AG recommends implementing a patching process that includes all cybersecurity controls. It is also advised to implement resilient, and if necessary, redundant controls to ensure continuation of business operations when controls require updates and/or downtime.
Secondly, these cybersecurity systems require monitoring to detect misuse. The number of users will be small (possibly from one team) and the access consistent from a limited set of assets. This makes monitoring and detection of potential misuse, abuse, or compromise significantly easier. In addition, monitoring of changes to configuration, policies and access control are useful. When compared against authorized change activity, this can be used to quickly identify unauthorized activity.
Help AG recommends implementing a Privilege Access Management (PAM) solution that will provide always-on protection, including facilities like user session recording and detailed auditing. Additionally, it is advised to monitor and detect attempts to bypass any PAM solution. These are an early waning to potential misuse and may indicate harvested credentials being used by an attacker.
DDoS Attacks continue to rise:
- 33k: Total Attacks
- 64%: Increase in Q2 2021
- 145.9 Gbps: Maximum Size
- 18 Hours,2 Minutes: Longest Attack
- DNS: Top Attack Type
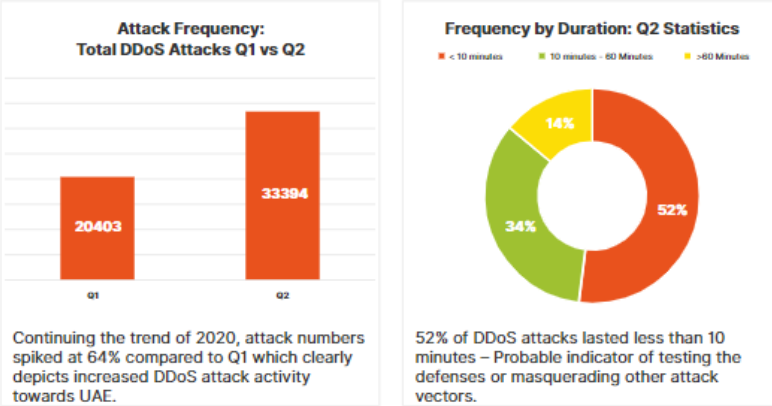
Continuing with the trends of 2020, DDoS attack numbers increased 64% in Q2 2021 compared to Q1 2021. Attack sizes remained relatively flat throughout the period, with sporadic large volume attacks being observed. Attackers seem to be focused on the duration of zero to ten minutes, as observed in 52% of attacks, while longer-duration attack numbers did not change appreciably.
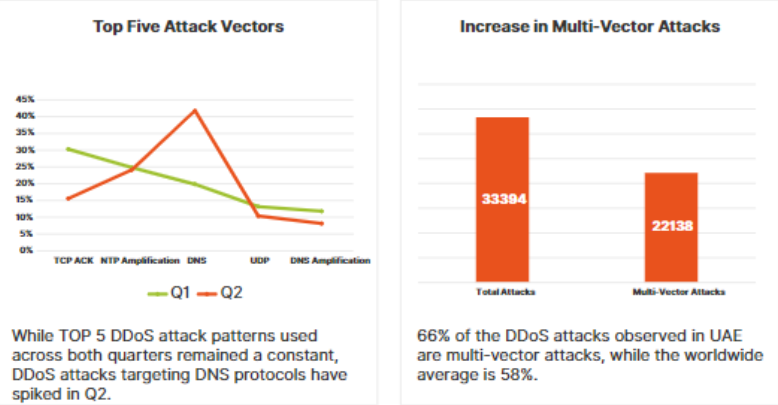
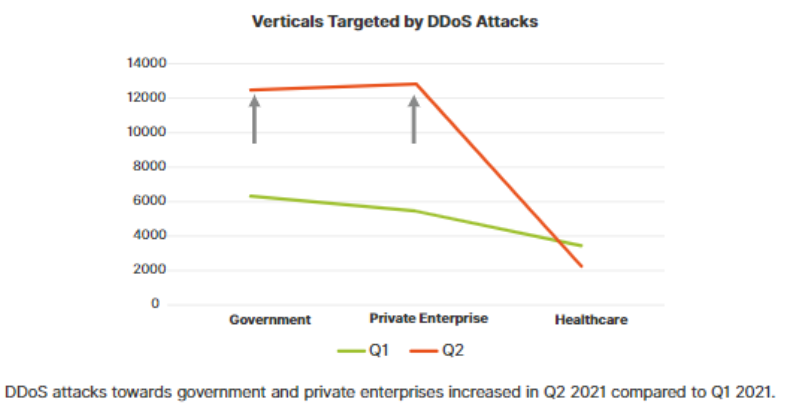
Meanwhile, attackers are finding value in pouring on faster, more difficult-to-mitigate, multi-vector attacks. 66% of the attacks observed in UAE were multi-vector attacks. 11 different attack vectors were used in a single attack targeting a UAE customer. Government institutions, private enterprises and healthcare remain the top targeted verticals within UAE. Attacks targeting the healthcare vertical remained static compared to Q1, while government and private enterprises have been subjected to increased attention from malicious actors. Though these three verticals remain top targets, persistent attacks targeting industry verticals such as finance, gaming and aviation were also observed.
DDoS Extortion campaigns in Q2
Fancy Lazarus DDoS Extortion Campaign
In May 2021, self-designated threat actor(s) ‘Fancy Lazarus’ began a new campaign of Distributed Denial of Service (DDoS) extortion attacks against organizations. The attacks are following a familiar pattern: after launching demonstration DDoS attacks, ‘Fancy Lazarus’ are threatening to follow up with a more devastating attack against critical assets unless the victim pays a demanded sum via Bitcoin cryptocurrency. The threat actor behind this campaign appears to be leveraging the success of the Lazarus Bear Amada (LBA) campaign.
Conclusion
Spurred by the pandemic, to stay relevant and ensure business continuity, organizations are fast tracking their digital transformation journeys. Attackers are continuing to discover and weaponize complex attack vectors to exploit the weaknesses exposed by this digital shift. DDoS extortion campaigns are becoming the new normal.
On-premise intelligent DDoS mitigation capabilities combined with cloud-based upstream DDoS mitigation services are the best bet for organizations to ensure maximum responsiveness and flexibility during an attack. Help AG account management teams and Managed Security Operations Center can be consulted with regards to selection of optimal countermeasures and deployments.









