SHOW ME THE MONEY, OR FORGET YOUR FILES
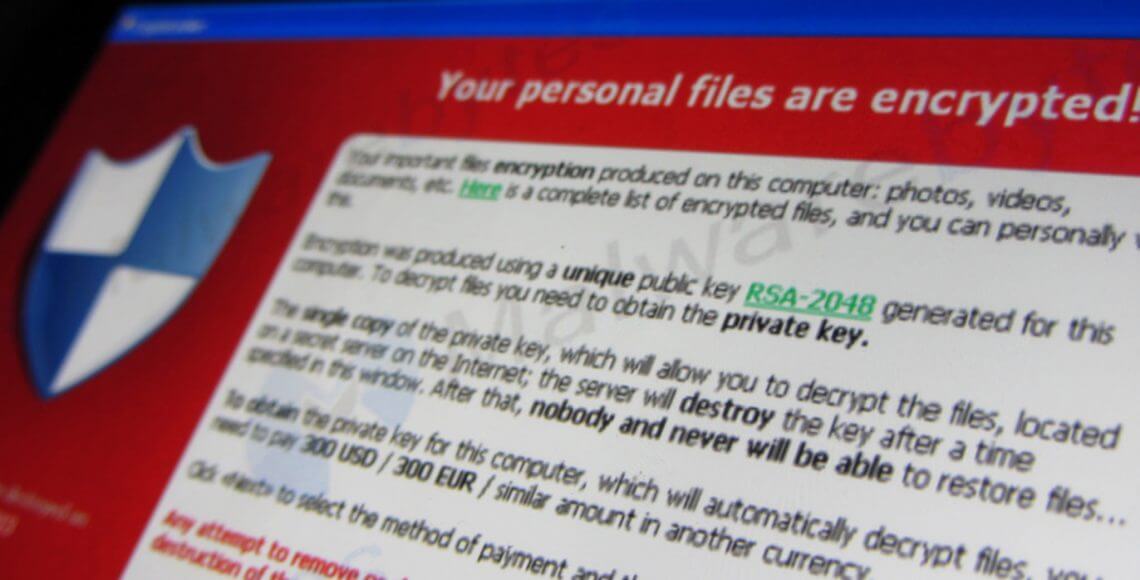
Photo Courtesy: Christiaan Colen
Growing fast and globally, ransomware – which is considered a form of scareware – is becoming everyone’s nightmare. It is the digital equivalent of a masked attacker jumping in front of you with a loaded gun asking you to give him everything you own or you risk your life. Ransomware is malware that installs itself on your computer and encrypts all your files, making them inaccessible until you have made a payment to decrypt them.
Types of Ransomware
Ransomware comes in different types: lock screen ransomware; encryption ransomware and leakware which is a cryptovirology attack that threatens to publish stolen information from the victim’s computer rather than deny access to it. The demands of payment, or ransoms, also come in various forms. Some claim you have done something illegal with your PC, others that a license has expired while the most obvious simply extort money to retrieve your files.
How You could Fall Victim
Ransomware can be downloaded onto your systems when you visit malicious or compromised websites. It can also arrive as a payload either dropped or downloaded by other malware, or even as attachments from spammed emails or through malvertisements.
According to recent studies, ransomware criminals are netting an estimate of $150million per year affecting home users and enterprises alike. When a ransomware attack occurs, it can easily elevate from potential data loss, to potential identity theft or even a data breach in the form of extortion.
Some of the most notable ransomware families seen in 2016 have come as executable macros Word documents, vulnerabilities on unpatched servers, and infections on removable drives (USBs), which makes the use of these drives very risky.
Can You Protect Yourself?
But when it comes to defense, there’s no silver bullet to stop ransomware yet one thing is certain, it is never recommended to pay the ransom. What you can do is to establish a multi-layered approach that prevents it from reaching networks and systems and this minimize the risk.
So what do you do when you don’t want to lose your data? It’s simple, keep another copy to retrieve the data. In short, what we can learn from the rise of ransomware is to always use BACKUP, following the 3 2 1 rule (3 copies, on 2 different media types, 1 stored offside).
Furthermore, malware usually attacks outdated software with known vulnerabilities, so make it a practice to patch and update your software. Also because of the precarious nature of how ransomware gets delivered, people are usually the weakest link and fall prey to clicking links in spam emails or downloading attachments that contain malicious code. Regular awareness and group policies to prevent downloading or executing unknown programs is an effective security measure.
At a more detailed level, here are some recommendations
- If you have Java installed, consider uninstalling it.
- Enable your pop-up blocker
- Avoid cracked and pirated programs
- Disable the loading of macros in your Office programs.
- Use secure passwords and two-factor authentication
- Disconnect from the internet if you believe you have received a ransomware message and restore your files from your backup
- Show hidden file extensions
- Filter executable files (.exes) in email
- Disable files running from AppData/LocalAppData folders
- Disable Remote Desktop Protocol
- Use System Restore to get back to a known, clean state
- Set the BIOS clock back
Finally and most importantly, keep your Incident Response & Business Continuity Plan ready. Attackers usually never give enough time for your organization to try to figure out how to unlock its data without paying the ransom. So it is very important to have a plan to map your critical assets and to define what needs to be done in case of an attack.
Blog by:
Sabrine Abu Sabaa, Cyber Security Strategic Consultant, Help AG






